The following process explains how to build your very own Zigbee CC2531 sniffer. Sniffing Zigbee traffic can be useful at times when you want to analyse the commands used by a device. Example you have Tuya device and you want to sniff the unique traffic when it talks back to the Tuya gateway as to help build drivers OR you have a ZigBee device or mesh issues and your trying to determine what is wrong.
Hardware Prerequisites
- Windows PC
- CC2531 with antenna
- CC debugger (note the kit above comes with the CC debugger as well)
1. Flashing the CC2531 stick
-
To flash the CC2531 stick it must be flashed with the sniffer firmware. Download the Zboss Sniffer firmware hex for the CC2531 USB dongle here. (note the software is free but you will need an account on their website to get access to the firmware etc also some people have found their activation email has taken some time to arrive but be patient). Save this file somewhere on your Windows PC.
-
Download and install the SmartRF Flash Programmer utility (DO NOT USE THE V2 VERSION) from here. This software is free but requires a Texas Instruments account in order to download. Once completed install the software to your Windows PC. You may also need the CC debugger driver for your Windows PC located here. Before continuing, verify that the CC Debugger driver has been installed correctly.
-
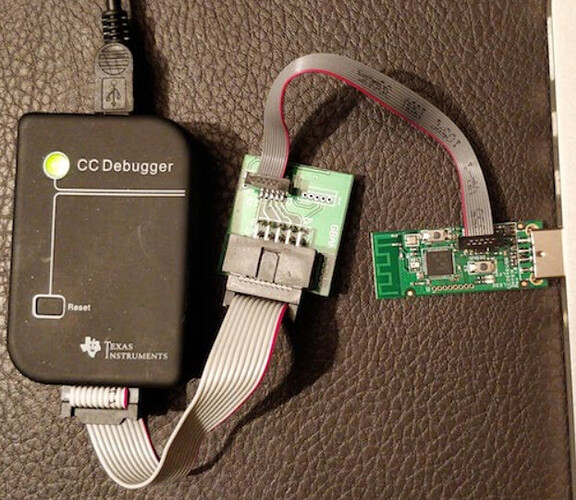
Connect your CC debugger to your CC2531 stick as per the below picture.
-
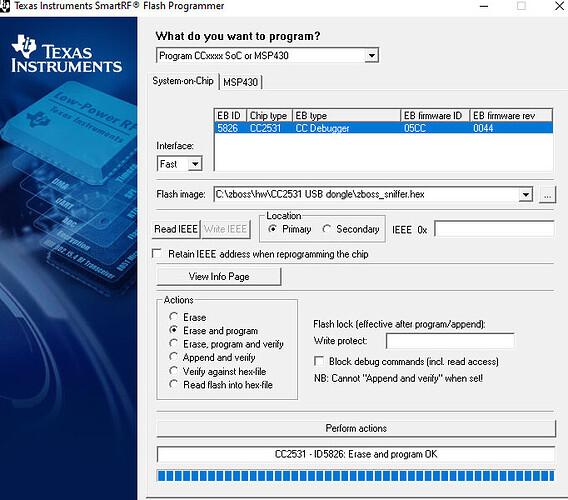
Plug the CC debugger and CC2531 stick into your Windows PC USB ports (yes both must be powered for this to work) and run the SmartRF Flash Programmer utility. If the light on the CC Debugger is RED press the reset button on the CC debugger. The light on the CC debugger should turn GREEN. In the flash image section locate your zboss_sniffer.hex firmware file and configure SmartRF Flash programmer utility like the below example picture. (note if you have issues flashing try changing the interface to slow from default fast)
-
Your CC2531 stick is now flashed with the zboss_sniffer.hex firmware. You can now unplug everything from your Windows PC and put your CC debugger away as you no longer require it.
2. Installing and configuring the Sniffing software and Sniff Zigbee Traffic
-
Download and install Wireshark from here.
-
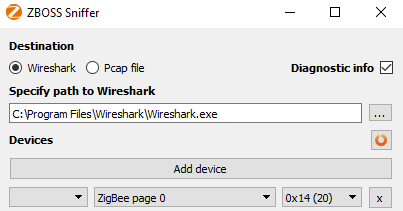
Download and install the Zboss sniffer Windows PC software from here. (Note at this stage you should already have an account on their website to access the download file). Zboss sniffer is a portable Windows PC software so just copy it somewhere like C:\zboss so you’ll run the GUI from C:\zboss\gui\zboss_sniffer.exe. When you run the GUI it should look like the below. Also for Zboss GUI make sure the correct Zigbee channel is set to your zigbee mesh channel (mine is 20).
-
Now plug in your CC2531 stick into your Windows PC USB port. (note it should come up as a COM port on your PC if it was flashed correctly)
-
Click on start in the Zboss sniffer GUI it will auto open Wireshark. Wireshark will then start to log the Zigbee messages, however as these messages are encrypted you will be required to add 2 encryption keys into Wireshark to decipher them:
-
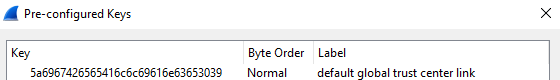
The first is the Trust Center link key, which is the same for (almost) every Zigbee network. Add the Trust Center link key into Wireshark by Edit → Preferences → Protocols → ZigBee. Set Security Level to AES-128 Encryption, 32-bit Integrity Protection and click on Edit. Click on + and add
5a6967426565416c6c69616e63653039with Byte Order Normal.
-
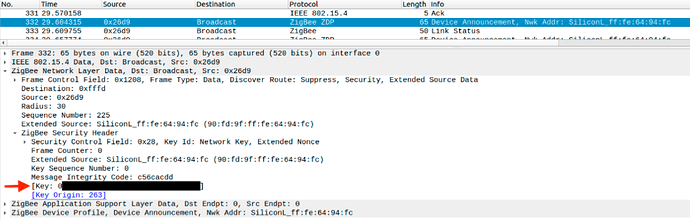
The second is the network encryption key (Transport Key). There is two ways this can be achieved. The network encryption key is exposed when a device joins the network. Pair a new Zigbee device to your network (or re-pair an existing one) and grab the message where the Info is Device Announcement….. Open the message and expand ZigBee Network Layer Data → ZigBee Security Header.
Copy the key value, as shown above and go to Edit → Preferences → Protocols → ZigBee → Edit and add the key with Byte Order Normal.
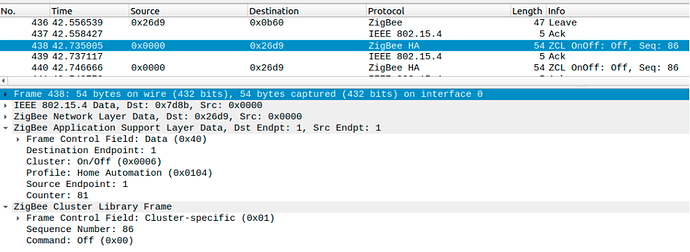
Now Wireshark is able to decrypt the messages. When e.g. turning on a light you will see a message similar to:
-
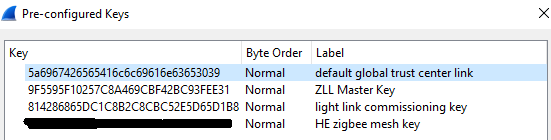
The third and fourth for things like Hue bridge as they use a different Trust Center link key you will need to copy into Wireshark by Edit → Preferences → Protocols → ZigBee. Set Security Level to AES-128 Encryption, 32-bit Integrity Protection and click on Edit. Click on + and add
814286865DC1C8B2C8CBC52E5D65D1B8with Byte Order Normal and call that light link commissioning key and also add ‘9F5595F10257C8A469CBF42BC93FEE31’ and call that ZLL Master Key. -
Once all your keys are added into Wireshark it should look something like this.
- You are all finished enjoy